


As such, organizations are making their vendors obtain System and Organization Controls (SOC) attestation reports, as mandated by SSAE 16 and SSAE 18.
A SOC report is a verifiable auditing report which is performed by a Certified Public Accountant (CPA) designated by the American Institute of Certified Public Accountants (AICPA). It is a collection of offered services of a CPA concerning the systematic controls in a service organization. A SOC report tells us if financial audits are performed or not; if audits are done as per the controls defined by the serviced company or not; and the effectiveness of the audits performed.
In brief, a SOC report is the compendium of safeguards built within the control base of the data and is also a check if those safeguards work or not.
If you are an organization which is regulated by the law, then you must be asking your vendors to provide a SOC report, as it becomes more critical for those vendors which you consider to be dealing with the high-risk operations of your business.
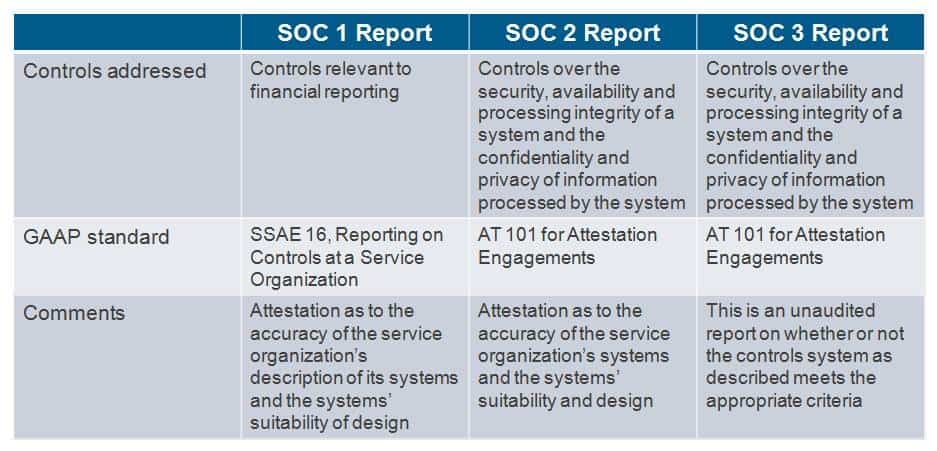
Some of the vendors provide a SOC 1 report, while some give SOC 2. Sometimes it might also happen that some of the vendors provide a combination of both. Not just this, but SOC 3 reports too exist. The differences are vast and are not evident to those people for whom Systems and Organizational Control is an unfamiliar domain.
What are SOC 1, SOC 2, and SOC 3 reports?
SOC 1 reports address a company's internal control over financial reporting, which pertains to the application of checks-and-limits.
By its very definition, as mandated by SSAE 18, SOC 1 is the audit of a third-party vendor's accounting and financial controls.
It is the metric of how well they keep up their books of accounts.
There are two types of SOC 1 reports - SOC 1 Type I and SOC 1 Type II. Type I pertains to the audit taken place on a particular point of time, that is, a specific single date. While a Type II report is more rigorous and is based on the testing of controls over a duration of time. Type II reports' metrics are always judged as more reliable as they pertain to the effectiveness of controls over a more extended period of time.

SOC 2 is the most sought-after report in this domain and a must if you are dealing with an IT vendor. It is quite common for
people to believe that SOC 2 is some upgrade over the SOC 1, which is entirely untrue. SOC 2 deals with the examination of the
controls of a service organization over, one or more of the ensuing Trust Service Criteria (TSC):
* Privacy
* Confidentiality
* Processing Integrity
* Availability
* Security
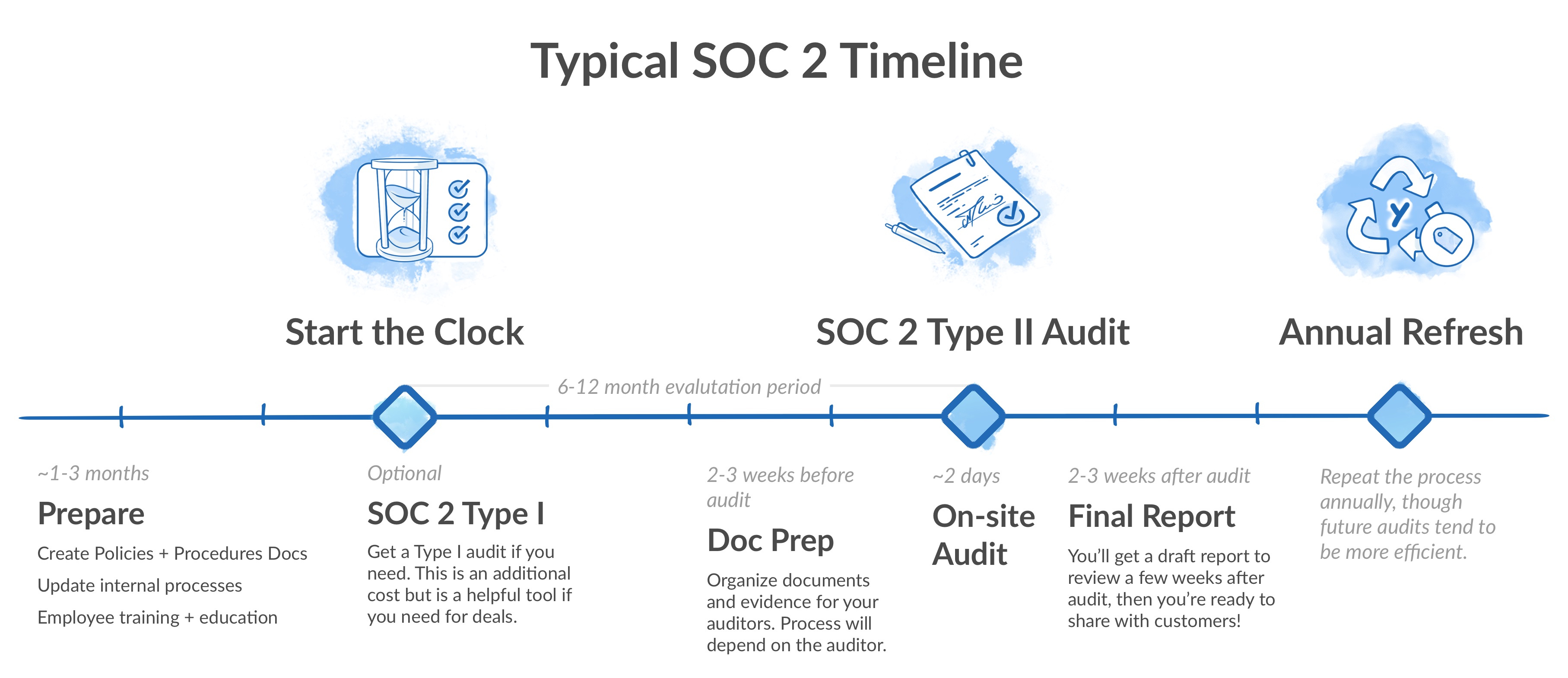
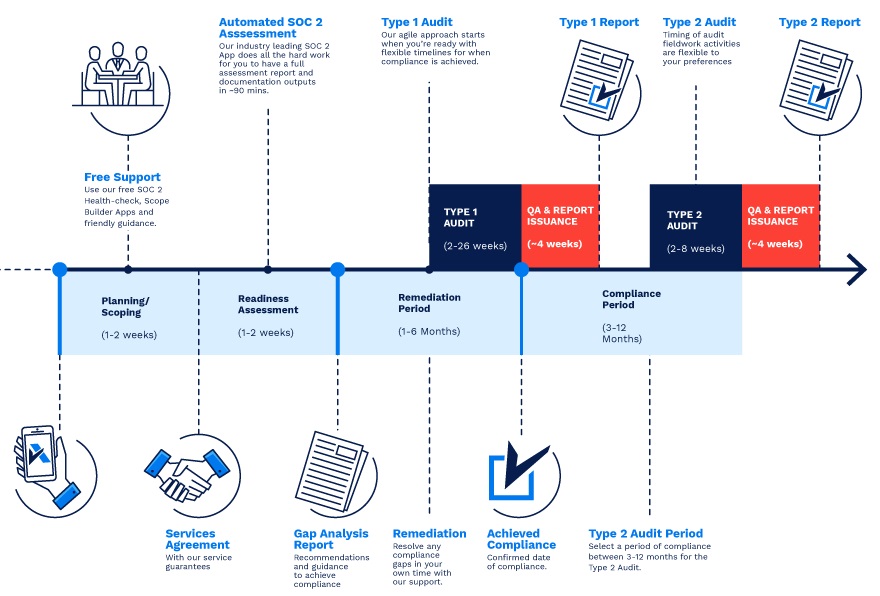
SOC 2 is built around the definition of a consistent set of parameters around the IT services which a third party provides to you. If you require to have a metric of a vendor's providence of private, confidential, available, and secure IT services - then, you need to ask for an independently audited and assessed SOC 2 report. Like SOC 1, SOC 2 too has two types - SOC 2 Type I and SOC 2 Type II.
Type I confirms that the controls exist. While Type II affirms that not just the controls are in place, but they actually work as well. Of course, SOC 2 Type II is a better representation of how well the vendor is doing for the protection and management of your data. But, the serviced party here has to be very clear about this that the SOC 2 Type II report is to be audited by an independent CPA.
A risk management strategy provides a structured and coherent approach to identifying, assessing and managing risk or uncertainties followed up by minimizing, monitoring and controlling the impact of risk realities or enhancing the opportunity potential by applying coordinated and economical resources.
Our experts partner with clients on corporate planning, providing perspective not only on immediate value and impact, but on long-term implications. We work closely with management and other advisers to leverage and complement their knowledge and ensure maximum impact, and actively support implementation and skill building.

